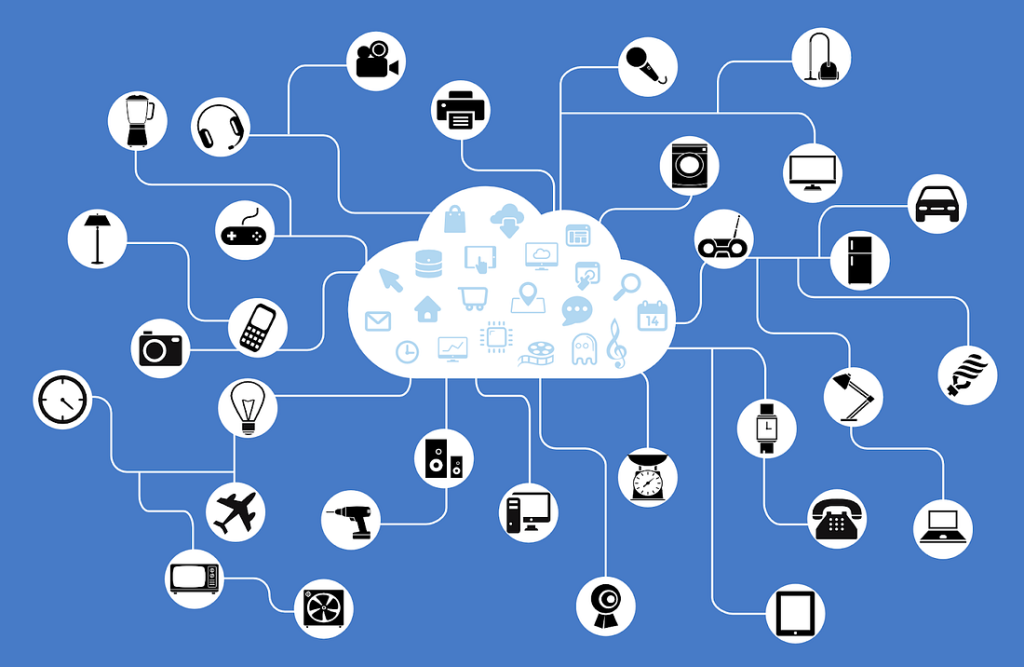
As a centralized storage and computing infrastructure, the cloud is accessible via the internet. Top benefits of cloud storage include scalability, accessibility, and cost-effectiveness. However, the cloud does come with a multitude of security risks. Those risks include:
- Lack of physical control
- Shared infrastructure
- Inadequate security measures
- Insider threats
- Dependence on the network
- Compliance concerns
- Data breaches
Lack of Physical Control
Cloud data and applications get stored in remote data centers. A third-party service provider manages these. There is limited control over the physical security of the data and systems a user can have. This lack of physical control is why the cloud is so vulnerable to cybercriminals.
Shared Infrastructure
To cut costs, cloud service providers often share infrastructure. A multitude of digital tenants can share the same hardware and network resources, boosting the risk of widespread data breaches. Compliance issues with regulated industries such as finance and healthcare can result in million-dollar fines. The only option to keep such sensitive info safe is to choose cloud service providers with strong security policies and protocols, including multi-tenant security measures, network segmentation and access controls.
Inadequate Security Measures
Cloud service providers must secure the infrastructure via encryption, access controls and security audits at consistent intervals. Encryption transforms plaintext to ciphertext via authorized parties who control access.
Security audits decrease the risk of data breaches. Secure third-party providers need strong policies and protocols to identify and remediate vulnerabilities. Multi-factor authentication also enhances the security of cloud environments.
Insider Threats
It isn’t always cybercriminals looking to access high-value data. Malicious insiders may want to negatively impact a company’s reputation. With access to sensitive information, theft and damage to the data systems can result.
The biggest risk with malicious insiders is their legitimate access to the information and infrastructure. Thorough background checks, heavily monitored access controls and consistent monitoring controls help mitigate this risk. Malicious insiders pose a significant threat because they have legitimate access to sensitive information and infrastructure. Access controls aim to restrict their access to only what is necessary, while monitoring controls are meant to detect and alert any suspicious activity. To minimize this risk, thorough background checks, closely monitored access controls, and continuous monitoring controls should be implemented.
Dependence On The Network
Clouds are powered by the internet, which means a network-based attack can be devastating. Cyberattacks can include Distributed Denial of Service attacks (DDoS) and man-in-the-middle attacks. This dependence on the network equates to vulnerability to network-based attacks.
DDoS attacks overload the network and make data unavailable, a horror when running a large-scale organization. Man-in-the-middle attacks intercept the transmission of data over the network, ruining confidentiality.
By exploiting vulnerabilities in the underlying network infrastructure, businesses can have a significant loss in productivity and a reputation in ruins. Third parties must harness the power of network segmentation and traffic filtering via firewalls and intrusion detection systems to block unauthorized access in hopes of protecting sensitive information.
Compliance Concerns
The healthcare and financial industries have a multitude of compliance concerns, including the Health Insurance Portability and Accountability Act (HIPAA). Any breach can result in fines, legal action, and damaged reputations.
Businesses should look for cloud service providers who are compliant and regularly audit their compliance. This can be done via data encryption and access controls.
Data Breaches
Customer data, financial information, and intellectual property are at risk in the cloud. A data breach can result in theft of bank account numbers, confidential business plans and trade secrets. Regular security audits and vulnerability assessments can prevent unauthorized access to sensitive information.
Harnessing the power of cloud technology carries the risk of countless potential security issues. Organizations should develop and implement a holistic security plan, including consistent security checks, complex encryption algorithms and restricted access. Cloud service providers must also be thoroughly vetted for exceptional security policies and procedures.
By taking advantage of these resources, cybersecurity professionals can stay ahead of any new developments or threats that may arise. Staying up-to-date with the latest advancements and changes in the ever-evolving field of cybersecurity is critical. With new technologies, security risks, and improved best practices, experts must stay informed and prepared for increasingly complex attacks.
ThriveDX offers a wide range of resources, such as ThriveDX-powered bootcamps along with security awareness training to upskill and reskill your workforce. Whether you’re looking to stay abreast of the everchanging cyber world on your own or expand your workforce’s knowledge and expertise on cyber threats, visit ThriveDX’s website to learn more.